Devon and Cornwall Linux user group meetings for January 2022
Also has details of other events organized by DCGLUG members
I am creating this post in order to consolidate previous meeting information in to one post.
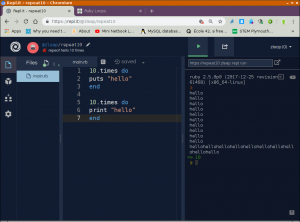
CODE CLUB
Code Club takes place on the First and Third Saturday of the month, as the First of Jan is new years day, there will be NO code club, and therefore the first club of 2022 will be on the THIRD Saturday. Please contact Paignton Library for information / booking.
STEM GROUP
Saturday 8th January 2022 @ Paignton Library from 11am
https://www.torbaylibraries.org.uk/web/arena/paigntonlibrary
Please book via the library, as we need to know numbers attending.
DCGLUG virtual meeting (jitsi)
Day / Date: Saturday 15/1/2022
Time: From 12:00 Location:
Online – Meeting jit.si link
Please see meetings page for more info or ask on IRC / Mailing list.
DCGLUG Plymouth Physical meeting
Day / Date : Saturday 22/1/2022
Time : 12:00
Location : Moments Cafe, Plymouth – Website
Please ask on e-mail discussion list for more information. We can also be found on #DCGLUG on the Libera.chat IRC network.
Dates / times are provided to the best of my ability, please contact Paul Sutton via the list if there is a problem.